September 22, 2022
What is passwordless authentication, and should you be using it?
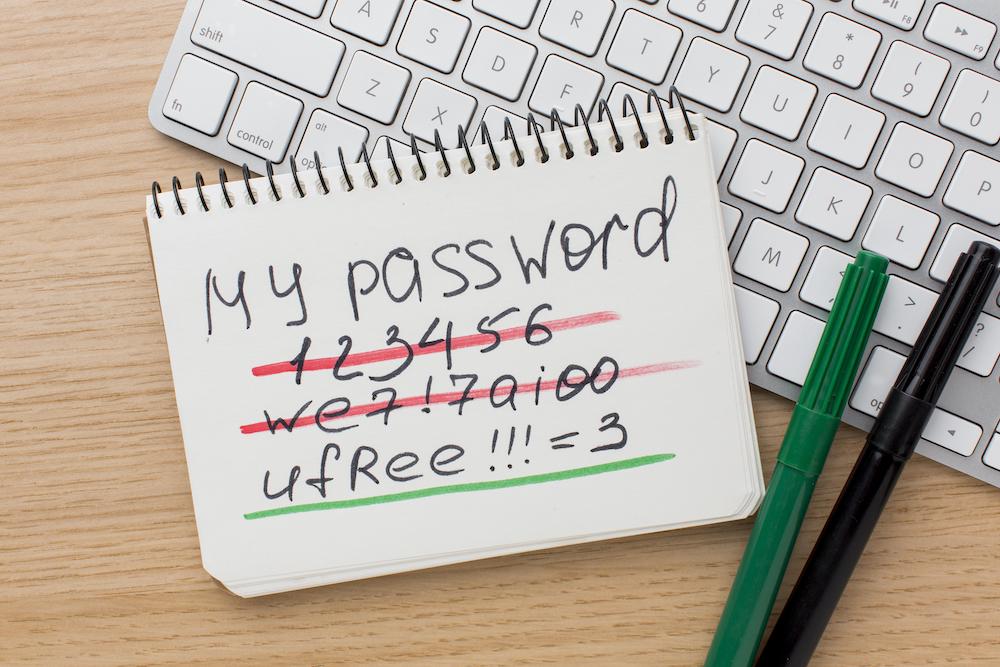
Passwords aren’t as simple as they used to be. Gone are the days of having your child’s birthday, mother’s maiden name, pets name, or favourite dessert as a password. There are now thousands if not hundreds of thousands of hackers worldwide and their methods of hacking and guessing people’s passwords are becoming more advanced.
To combat this, people are encouraged to create strong and different passwords for each of their accounts.
However, with the average person today possessing tens if not hundreds of accounts, they can struggle to keep strong passwords for each account – meaning they take shortcuts. According to GetApp, 56% of UK users reuse their passwords. And according to IT Governance, 23 million people are still using ‘123456’ as their password.
So despite more than ten years of guidance, people are still doing what’s easy – using short and quick passwords.
So as a security industry, we’ve thought of a new way – no passwords. We call it passwordless.
Here, we outline what passwordless authentication is and whether your business should be using it.
What is passwordless authentication?
As the name suggests, passwordless authentication allows users to verify their identity to enter their accounts without the need of entering a password.
Multi-factor authentication is still needed of course (see our blog on that too if you haven’t already). But instead of the factors being:
- Something you know (password or pin)
- Something you have (your phone, your security key, your ID card)
- Something you are (your biometrics)
We get rid of the something you know. Humans are forgetful anyway – so something you knew before, might not be something you know now!
Along with getting rid of the “something you know”, Passwordless approaches are often combined with Single Sign-On (SSO). This is where you can sign in once to a central system that then gives you access to other systems without signing in again.
Along side single-sign on approaches, another way lots of services now go passwordless quickly and easily is by using magic links. This is where you get a one-time link emailed to you when you try to login. Click the link in the email and you’re in!
No know: just have and are.
So, if we exclude the Know element. And go with the Have and Are factors of authentication what are we left with. Let’s explore:
Biometrics
Biometrics grant a user access by using biological factors instead of entering a password. Examples of this are through fingerprints or facial recognition, the latter of which is commonly used with smartphones. This is an incredibly secure form of verification, as facial features and fingerprints are unique to you and hard for an attacker to steal or imitate!
(Note most facial recognition systems also have ‘liveness-detection’ built in so that you can’t hold up a photo of someone to get in!)
Single sign-on (SSO)
SSO allows users to enter several software systems with just a single centralised login. As a result, if a business has an SSO system in place, users can skip entering multiple passwords for every application or website they want to gain access to. Not only does this create a more seamless experience for the user, but it also eliminates the risk of hackers guessing your password and infiltrating your system, as there aren’t any passwords to guess.
Typically, SSO only works for when you log into your company accounts as it’s a service your company pays for. But it could also be hosted by other well-known online consumer services such as Sign in with Microsoft, Facebook or Google.
Magic links
Magic links allow users to log into their accounts without typing a password. Instead, authentication is granted by clicking a link emailed to the user. Like SSO, this authentication process is easier for people who struggle with constantly remembering passwords. If an attacker wants to gain access to your accounts, they will need to gain access to your email first. This is another challenge they need to overcome, making it more secure than just having a password to gain access.
This is arguably another “something you have” authentication factor because it proves you have access to your email account. It may or may not be multi-factor authentication as it depends how secure your inbox is! But it certainly achieves a login without a password. It also means the service you are logging into doesn’t need to store your password – which is the best way to avoid a password leak.
Should you be using passwordless authentication?
Passwordless authentication brings with it some notable advantages and disadvantages.
In particular, the key advantage of Passwordless authentication is convenience for the user. It speeds up the login process and means the user doesn’t need to remember a password. Nor does the user need to change their password regularly. This saves the business wasted time.
Likewise, not storing passwords in a database somewhere means the company will not be able to lose those passwords in a data breach. Elimination of risk is always better than risk reduction.
However, whilst passwordless is an undoubtedly a useful asset in your IT security posture, the process of turning your entire business’s network to passwordless does take some time. What’s more, businesses using legacy software that requires passwords might not be able to adapt to passwordless easily.
Still unsure of whether to add passwordless authentication to your IT security posture? Get in touch with us, and we can help you decide if it’s right for your business.